There are many incidents where attacker hacks the AWS account and abuse it for their purpose or just for fun. I came across this post on Quora, where the user’s AWS account was hacked and received a $50,000 bill! Single sensitive information leakage can cost you heavily and damage your reputation. So how do you ensure you’ve taken all the necessary steps to protect the AWS account? One way you can do is to follow industry security guidelines manually, which is time-consuming and prone to human error. Or you can use the following SaaS (Software-as-a-service) to automatically audit your AWS platform for the security loophole and misconfiguration. Note: Below vulnerability scanner are specifically for AWS Cloud and not for website or web applications. Let’s explore what options we have…
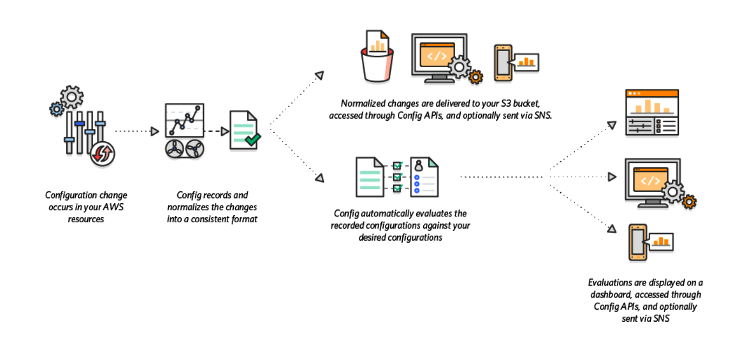
AWS Config
AWS Config is an effective tool for assessing, evaluating, recording, auditing configurations of the resources in your AWS environment. It simplifies security analysis, compliance auditing, operational troubleshooting, and change management. key features include
Provide continuous monitoring, assessment, and recording of the resource configurations.Enables you to discover resources, record the configurations in your AWS environment, and keep important information about their changes and deletions.Automate the evaluation of the recorded AWS resource configurations against expected values.Quickly troubleshoot operational issues by determining the recent resource configuration changes causing the problems.Supports change management processes by keeping track of the created, updated, and deleted resources while notifying you about any modification.
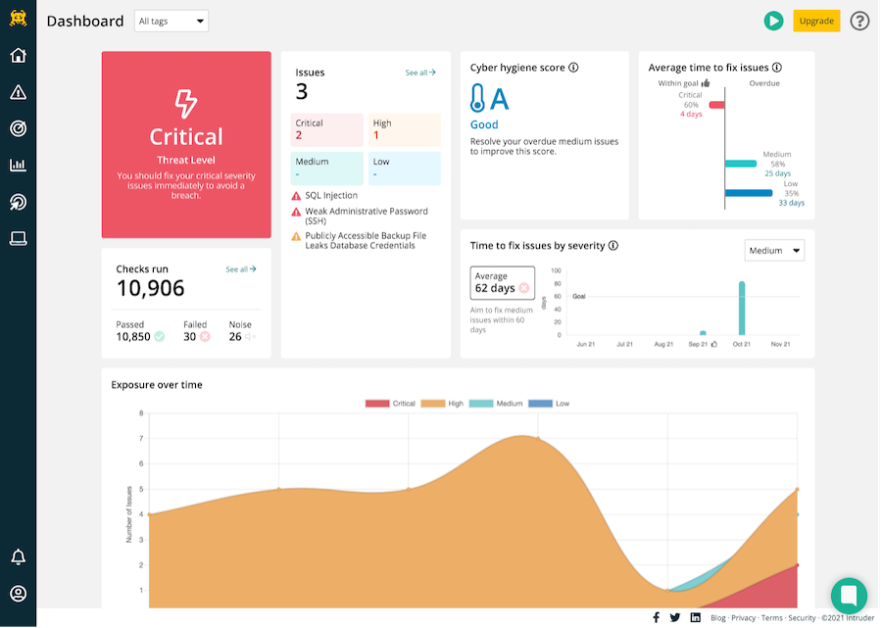
Intruder
Intruder is a modern vulnerability scanner, designed from day one to work seamlessly with the three major cloud providers, AWS, GCP, and Azure. It is enterprise-ready and offers a government & bank-level security scanning engine without complexity. Intruder makes cloud security a breeze by allowing you to easily monitor your cloud systems, discover new assets, and automatically synchronize your scan targets. It continuously observes what you expose to the Internet and sends notifications about important changes, such as when open ports and services change, which, if unnoticed, could lead to a security breach. Unlike some cloud-only vulnerability scanners though, Intruder is able to seamlessly monitor your traditional edge networks, web applications, and internal environments too, for an all-in-one effortless vulnerability management experience. Its robust security checks include identifying:
Missing patchesMisconfigurationsWeb application issues such as OWASP top 10, SQL injection & cross-site scriptingCMS issues
Intruder proactively scans your systems for new vulnerabilities, keeping you protected against the very latest threats. This kind of proactive action is essential for busy teams that don’t have time for manual research. You can give Intruder a try for 30 days for free.
Astra Pentest
Astra Pentest is the best-in-the-industry cloud security suite that combines a vulnerability scanner with automated and manual penetration testing to ensure optimum level of security of AWS infrastructure against any vulnerability exploits. It is designed to comprehensively test for security weaknesses in your AWS with over 3000 test cases and ensures all the requirements for regulatory compliance are met. Key Features of Astra Pentest:
Automated Vulnerability Scanner with an option to scan behind login pages using Astra Login RecorderRisk-based Vulnerability Management to prioritize and fix vulnerabilities on timeAutomated and Manual Penetration Testing with our 3000 test casesDetailed vulnerability analysis with potential loss in $, CVSS score, severity and impactSeparate Pentest Compliance dashboard with distributed test cases for SOC2, ISO 27001, PCI-DSS and HIPAAIntegration with your CI/CD and Apps that converts your DevOps to DevSecOps Detailed vulnerability reports (Email and PDF reporting available)Publicly verifiable Pentest Certificate24×7 Support option available
Uncover vulnerabilities before hackers with our intelligent scanner and manage your entire security from a CXO and developer-friendly dashboard. Select a plan as per your needs.
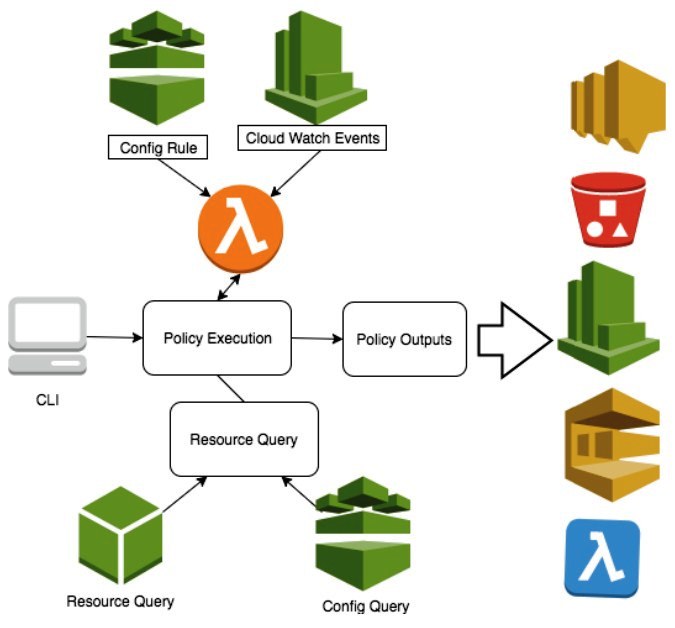
Cloud Custodian
Cloud Custodian is a flexible open-source rules engine for managing the AWS cloud resources and accounts to ensure security and policy compliance. This allows you to manage and optimize security, costs, and governance of your AWS cloud environment. Cloud Custodian key features
Providing real-time compliance checks and report on violations.It allows you to control costs by managing the unused and off-hour resources.A flexible deployment that allows you to run the tool on an instance, locally or serverless.Ability to manage users and enforce security policies in the AWS cloud environmentConsolidates several functions into a flexible, lightweight tool with unified metrics and reporting.
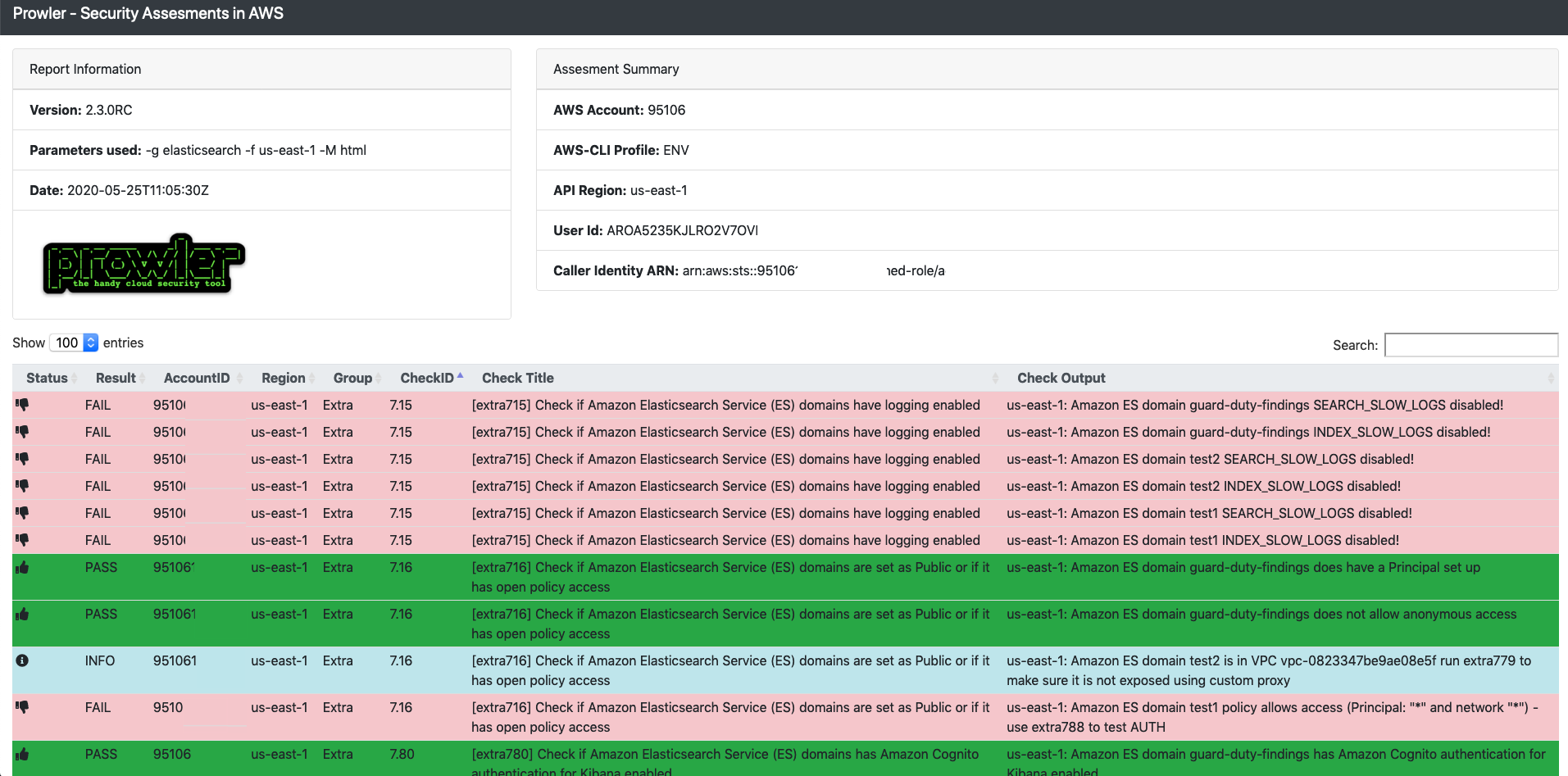
Prowler
Prowler is an AWS account’s security configuration assessment, auditing, and hardening tool that also checks compliance with the CIS AWS Foundations security standards. Further, the tool performs over 100 additional checks, including HIPAA, GRDR, forensics readiness, trust boundaries, and more. Highlights
Comprehensive assessment of the security posture of your AWS accountsIntegrate with other tools such as Cloud Security Suite, Telegram, etc.Check multiple AWS accounts in parallelRun specific checks without having to perform the entire testIdentify assets not covered by security systems.
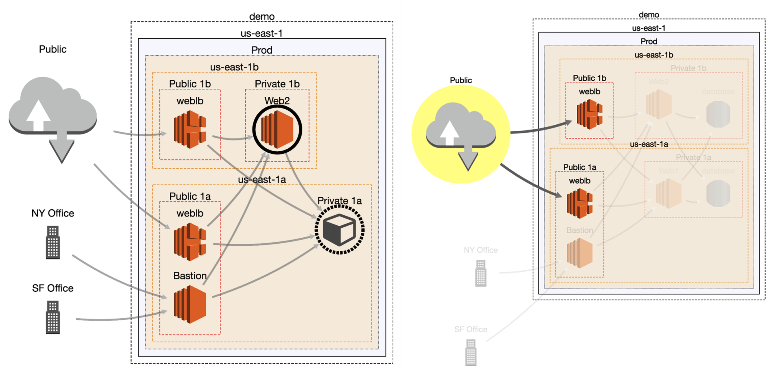
Cloudmapper
Cloudmapper is an open-source tool that enables you to analyze and build an interactive visualization of assets, services, and other components in your AWS environment. Generally, the tool allows developers to check and understand the type of environments they have built. It does this by collecting the data from your AWS accounts and then converts it into a browser-accessible format. Typically, the Cloudmapper outputs the analysis in the form of network diagrams for the AWS cloud environments. The visual presentation enables you to understand your accounts, how they relate to cloud resources as well as establish if there are misconfiguration or other issues. This allows you to
See the complexity of the AWS account, size, and regions it serves, etc.Establish the resources that can communicate with each within the environmentPerform security audits, and easily share the analysis information.Identify publicly exposed resources
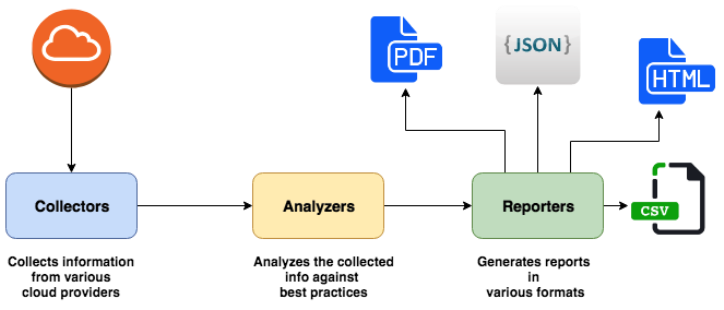
Cloud Reports
Cloud reports from Tensult is a node.js based open source tool for collecting and analyzing a wide range of information from various cloud components. The tool compares the findings against the best practices. It then generates reports, which are usually in HTML, CSV, JSON, or PDF, to show the different AWS services running along with the best practices you should follow. This also contains issues it has identified as well as their impact on your services. The HTML reports are usually accessible via a web browser, while those in JSON, CSV, and PDF are stored on a folder. Each of these has a timestamp for easy identification and access when running multiple scans.
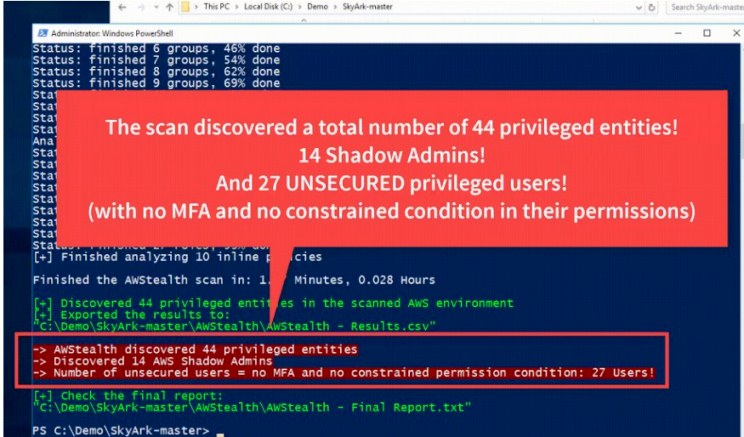
AWStealth
AWStealth is a security that tool teams use to discover the most privileged entities in the AWS cloud environment. The scan results show the users with excessive, risky, or sensitive permissions. And this enables the security teams to identify the most privileged accounts that they need to properly secure from potential attacks and exploits. Typical AWS entities with sensitive privileges that should be on the radar include the straight-forward admins as well as the risky shadow admins. The AWStealth thus enables the security teams to prevent threats arising from the shadow admins and other privileged account vulnerabilities.
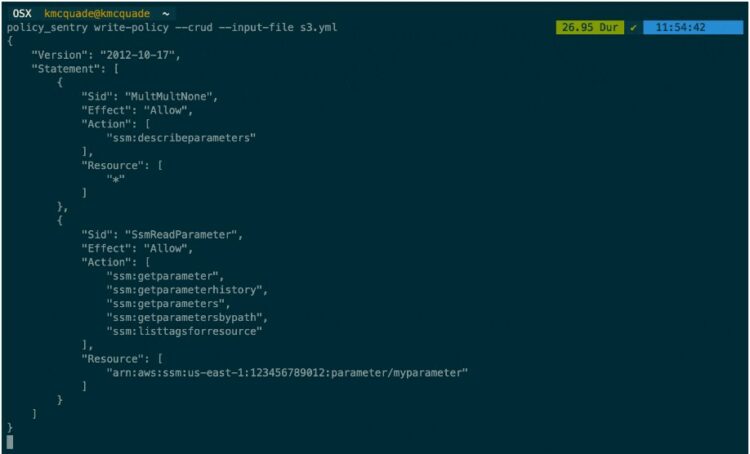
Salesforce Policy sentry
Policy sentry is an AWS IAM privilege management tool. It has an IAM least privilege policy generator, an audit mechanism, and an analysis database. The tool compiles database tables according to the AIM documentation about the resources, actions, and condition keys. It then uses this data to create IAM least-privilege policies. Highlights
Simplifies writing of security-based IAM policiesLimit the impact of a security breach since an attacker who accesses the system with a user’s credentials will only have the least privileges that cannot perform administrative tasks.Automatically and easily create secure IAM policies hence eliminate the tedious manual based tests that require higher levels of technical expertise.
Komiser
Komiser is a comprehensive inspection and analysis tool that helps you to monitor and control expenses for your AWS cloud platform. The open-source cost optimization tool can inspect the cloud platform and check for a wide range of configuration and cost issues. This discovers any hidden costs and provides you with recommendations to help you save and remain within budget. Key features
It enables you to analyze and manage usage, cost, security, and compliance of your AWS platform from one place and in real-time.Provides you with the visibility of all the services you are usingIdentify and address vulnerabilities as well as compliance issues in the AWS configurations and environment.Get visibility into all your services and how to control costs and maximize ROI.
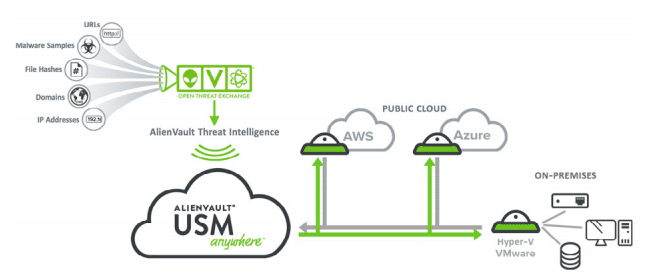
Alien Vault
Alien Vault USM (Unified Security Management), one of the market leaders in SIEM (Security Information and Event Management) solution for AWS. USM is a single security monitoring platform to provide visibility of what’s happening so you can take full control of AWS cloud and manage risk. Some of the essential inbuilt features are:
Monitoring & alerting for S3 & ELB logs, CloudTrail, File integrity, VPC flowEvent correlationAsset discovery using network, API, software & serviceVulnerability scanning for network, cloud & infrastructureIntrusion detection for cloud, network, host
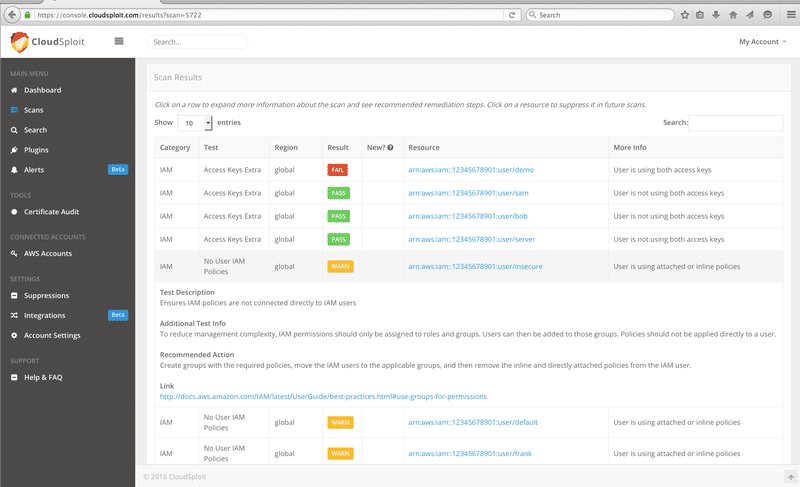
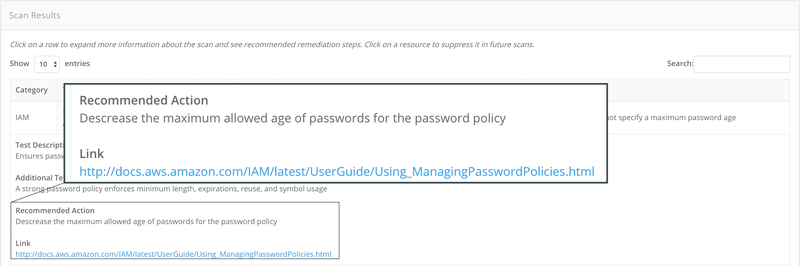
CloudSploit
CloudSploit is capable of detecting hundreds of threats in the AWS account by automated security scanning and configuration monitoring. You can use CloudSploit in every AWS region, and it’s not just provide scanning results but also the recommendation to fix the issues. CloudSploit offers API, which is useful if you are looking to integrate security scanning in your application. A good thing is you don’t need to install any agent on your server to be monitored. You can get it started in FREE for unlimited on-demand scans. And if you are looking for an automated scan, risk finding emails, real-time event streams, etc. then you got to pay for it.
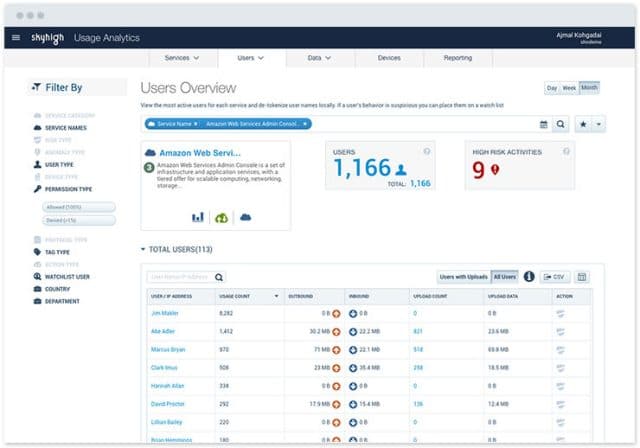
Skyhigh
Skyhigh, provide comprehensive security monitoring, auditing, compliance, and remediation for AWS infrastructure. Some of the essential features of Skyhigh are:
Complete audit trail of users activityDetect insider threats, compromised accountsCompliance, user permission, and security configuration auditingEnforce data loss prevention policiesCloud activity monitoringIAM, account access, user behavior analyticsIntegration with SIEM and IDMMulti-tier remediation
It supports a forensic investigation and automatically includes threats resolution data into self-learning for improved detection accuracy.
Qualys
Qualys, one of the industry leaders in vulnerability scanner platform for website, network provide total visibility of AWS cloud to secure and compile from internal and external policies. Qualys provides a cloud agent that can be installed either on EC2 or at the source into AMI for automated asset discovery, classification, monitoring, and vulnerability remediation.
ScoutSuite
ScoutSuite is a python based open-source tool to view the security posture of the AWS environment. It fetches CloudTrail, S3, AMI, EC2, etc. data and reports it in HTML format. Risk items are categorized automatically and denoted in danger and warning with red and yellow color, respectively.
Alert Logic
Improve your AWS security posture with Alert Logic Cloud Insight. Alert Logic is capable of inspecting full-stack infrastructure, including network, open-source, enterprise software against more than 90000 known vulnerabilities. Some of the essential Alert Logic key capabilities are:
Visual topology map for faster prioritizationRemediation prioritization based on the severity of vulnerabilitiesTrack improvement trendsEasy integration with SecOps & DevOps using RESTful APIAgentless comprehensive checks
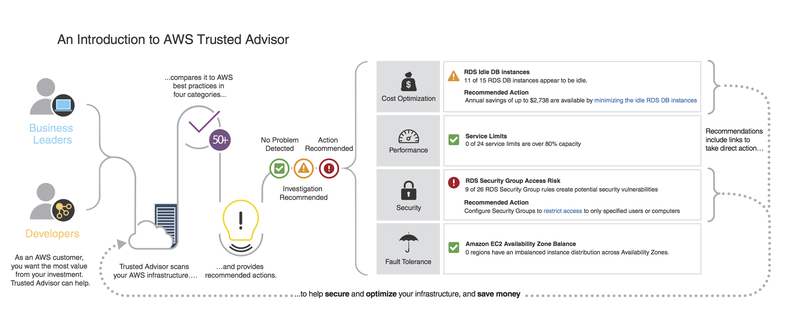
AWS Trusted Advisor
The list won’t be complete without mentioning AWS Trusted Advisor, a real-time guide to improve security, reduce cost by following AWS best practices.
Conclusion
AWS provides security on core infrastructure, but what you deploy, configure is your responsibility. I hope above listed AWS security scanning solution helps you to keep your AWS cloud environment secure & cost-effective.